Please Upload Files in Pretalx
Our File Drop is in another system!
This used to be a file drop interface that we translation angels used to gather support material that helps us provide our simultaneous interpretations.
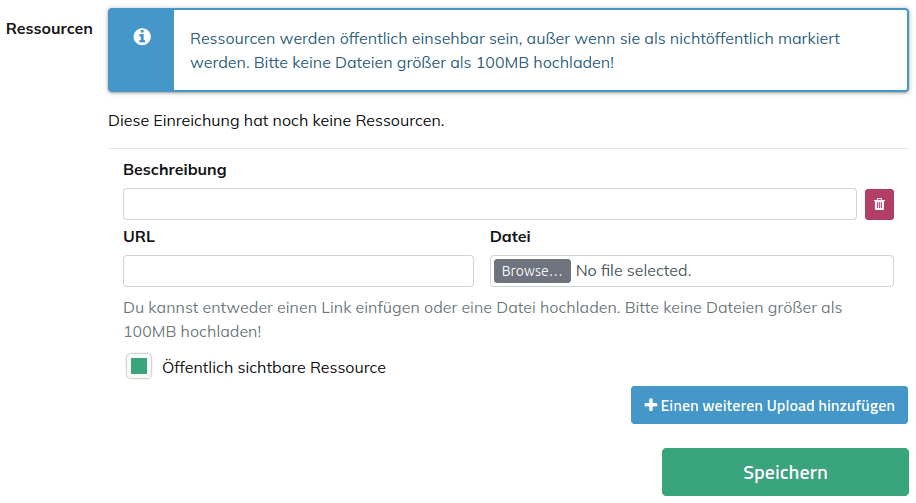
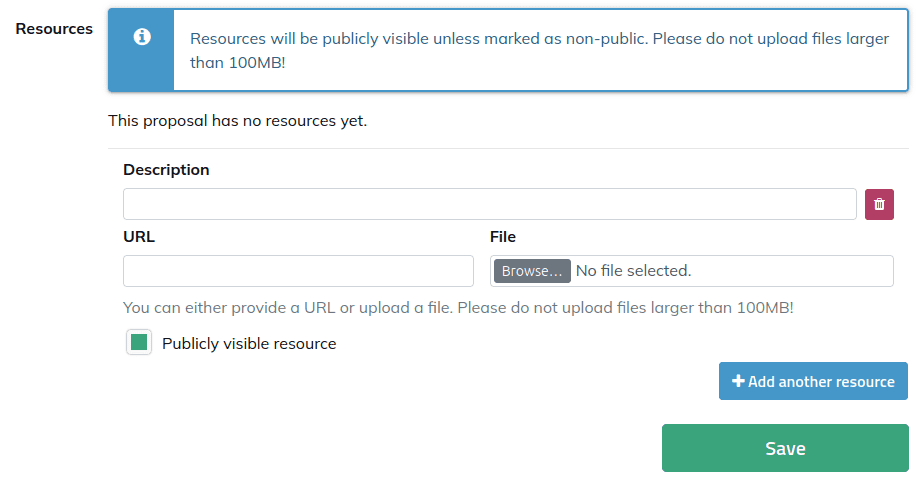
Starting at 39c3, you can upload scripts, slides, notes and all supporting material directly in Pretalx. You can choose if you would like to keep files for internal use or make them public.
Where do I do this?
If you have questions or would like to get in touch with us directly, email us at hello@c3lingo.org or follow c3lingo on Mastodon.